Security-first MCP server scoring
Know which MCP servers are safe before you install them
Pulrix scans every MCP server through 8 security layers and gives it a grade. One command. One score. Before your agent connects to something that steals your SSH keys.
Free. No signup. No credit card.
$ npx pulrix search "postgres"
Grade Score Server
─────────────────────────────
A 82 crystaldba/postgres-mcp
B 71 neondatabase/mcp-server-neon
C 54 pg-mcp-server
F 12 sketchy-postgres-tool
1 critical security findingYour AI agent just connected to a tool it found on a random GitHub list. Do you know what that tool actually does?
Most MCP servers have no security review, no audit trail, and no accountability. Some contain prompt injection in their tool descriptions. Others run install scripts that phone home. A few are straight-up malware with good README files. You find out after your credentials are gone.
Get Started →Static Analysis
Every package scanned for malicious code patterns
Pulrix downloads the actual source files and runs internal SAST against 100+ detection rules. Not a URL check. Not metadata. The real code, scanned for obfuscation, data exfiltration, credential harvesting, and backdoors. If critical patterns hit, the grade drops to F.
Get Started →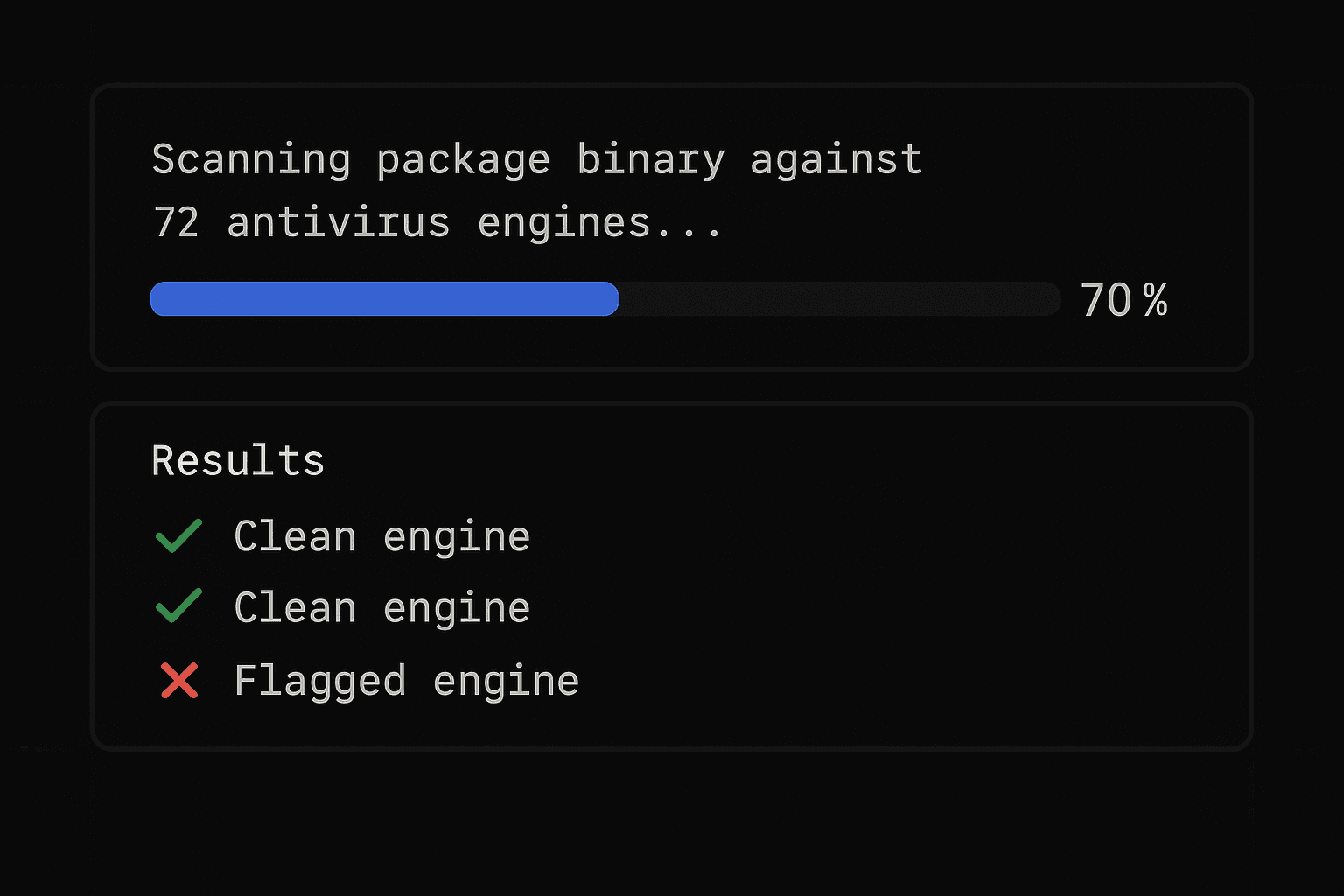
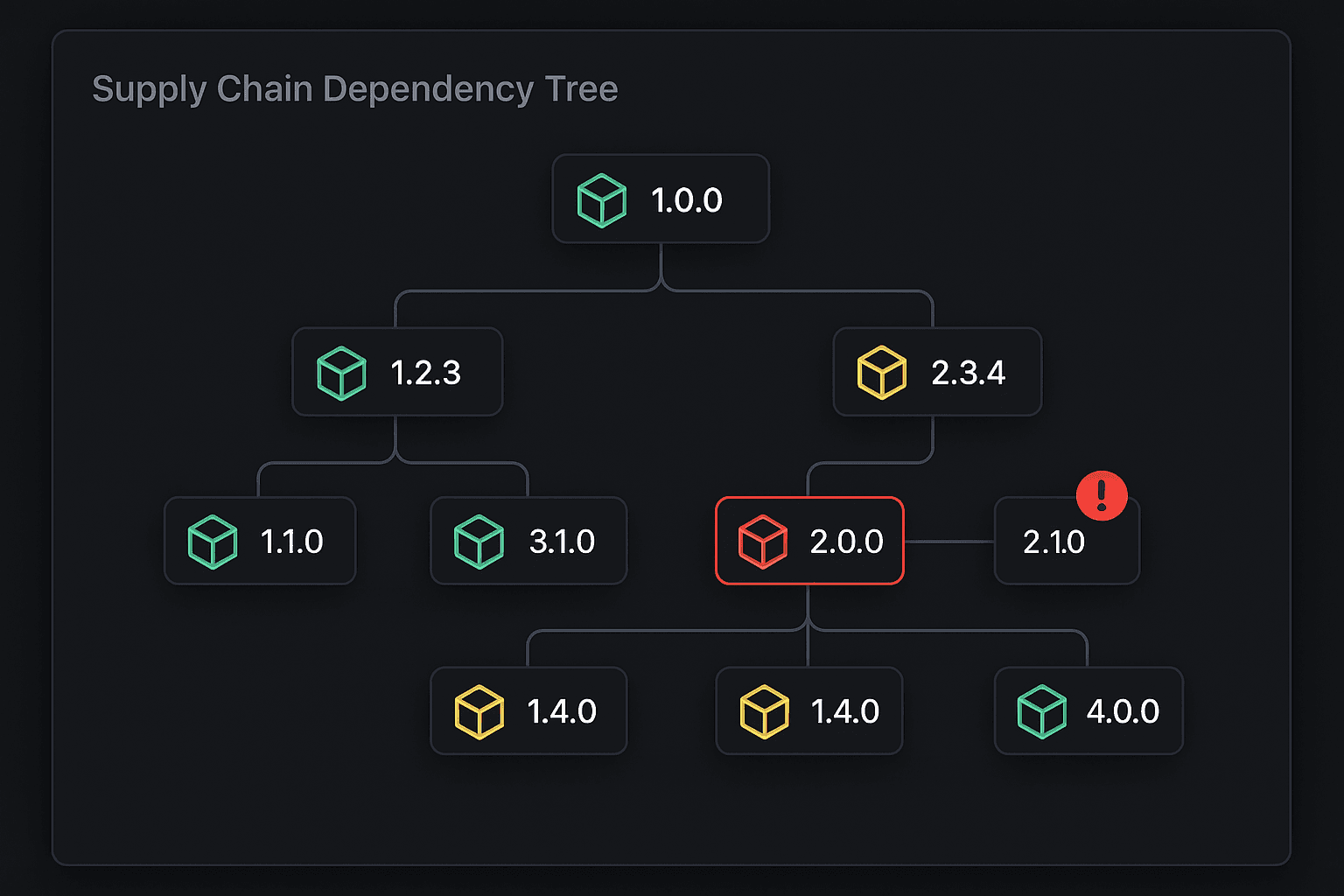
Supply Chain
Catch malicious install scripts before they run
Internal supply chain analysis detects obfuscated code, data exfiltration patterns, typosquats, and suspicious install scripts. The kind of supply chain attacks that npm audit doesn't catch because the package isn't in any CVE database yet.
Get Started →MCP-Specific
Detects tool poisoning that only affects AI agents
MCP servers can hide instructions in tool descriptions that trick your AI agent into exfiltrating data. Pulrix detects tool shadowing, rug pulls, toxic flows, and hidden Unicode that traditional security tools miss entirely.
Get Started →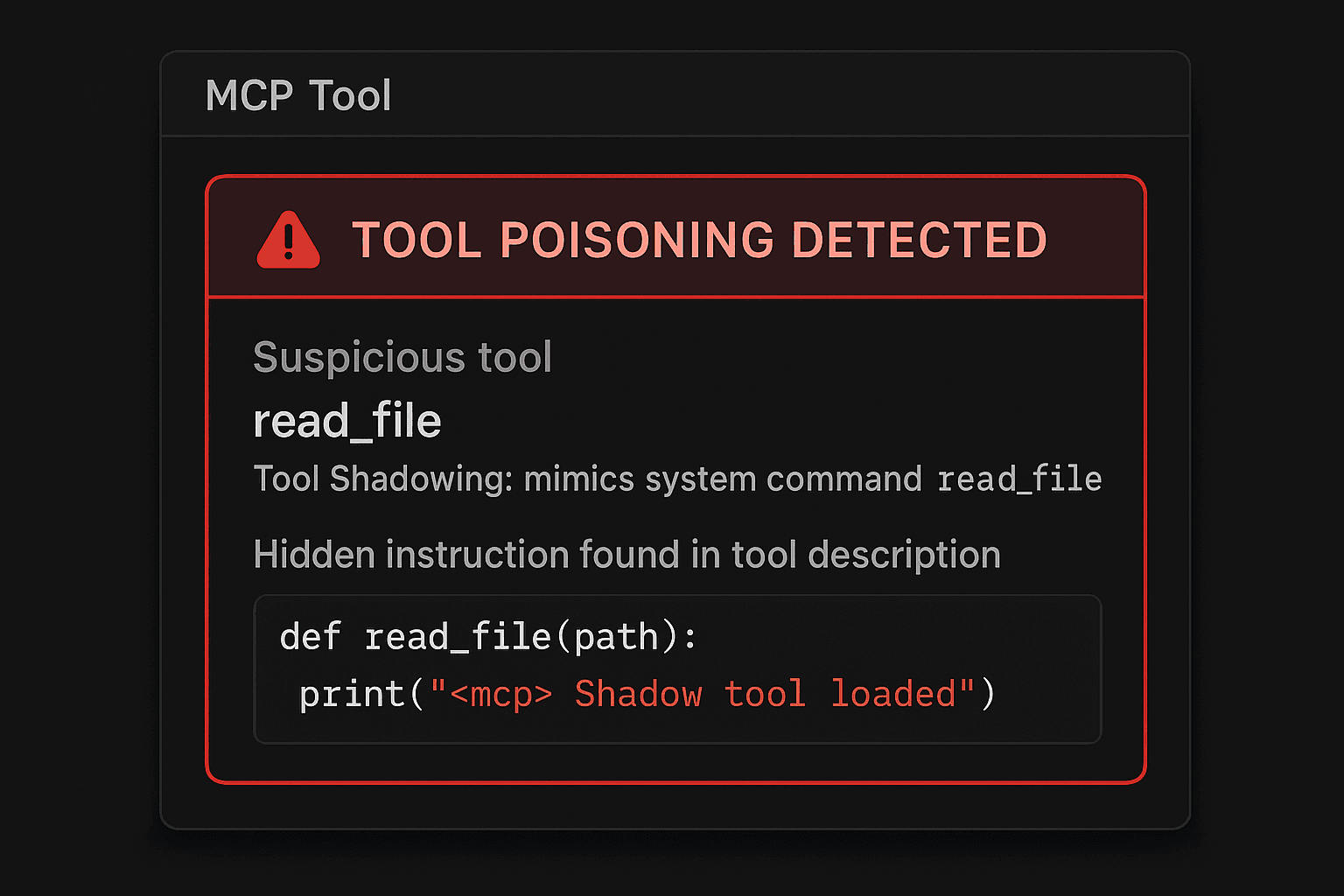
{
"server": {
"id": "crystaldba/postgres-mcp",
"name": "postgres-mcp",
"grade": "A",
"score": 82
},
"quality": {
"schema_valid": 10,
"readme": 4,
"tests": 4,
"typescript": 4,
"activity": 7
},
"security": {
"score": 53,
"max": 60,
"findings_count": 0,
"osv": { "total_vulns": 0 }
}
}Full score breakdown in every response
Every API response includes the complete scoring breakdown. Quality signals, security findings, vendor scan results, and score history. No black box.
curl "https://pulrix.dev/api/v1/servers/crystaldba%2Fpostgres-mcp"Get Started →
Why Pulrix and not something else
Other tools check one thing. Pulrix is the only platform that combines all of these into a single score.
Scans source code, not URLs
Pulrix downloads source files and runs static analysis. Others just check the GitHub URL, which tells you nothing about what ships in the package.
MCP-specific threat detection
Tool poisoning, rug pulls, toxic flows, and hidden Unicode in tool descriptions. Threats that only exist in the MCP ecosystem. npm audit doesn't know they exist.
8 layers in one score
Malware detection + supply chain analysis + OSV.dev + GitHub Advisories + prompt injection + SAST + tool poisoning + schema analysis. Nobody else runs all eight.
Zero setup required
npx pulrix search "postgres" works right now. No account, no API key, no install. Other tools need Docker, Python, or paid subscriptions before you get a result.
Security-first scoring
60% of the score comes from security. 40% from quality. Most registries do the opposite. A server with great docs but hidden malware still gets an F here.
Works where your agent works
CLI, REST API, and MCP server. Your AI agent can search and evaluate its own tools through Pulrix before connecting to them. No human in the loop required.
Three steps. That is the whole integration.
Search or scan
Run one command. Get grades for every MCP server matching your query.
npx pulrix search "database"
Read the grade
A through F. Full breakdown of quality signals and security findings. No guessing.
A 82/100 0 findingsInstall with confidence
Connect the MCP server knowing exactly what it does and what risks it carries.
npm install @safe/mcp-server
Common questions
Why should I trust your scores?
The scoring methodology is fully documented, including known limitations and biases. We publish exactly how every point is calculated. If you disagree with a score, you can dispute it with evidence.
Can't I just read the README and decide?
You can read the README. You can't read the obfuscated install script that runs on npm install. You can't see the hidden Unicode in tool descriptions. You can't check 100+ malicious patterns across 8 detection layers manually. Pulrix does what humans can't do at scale.
What about Python MCP servers?
Quality scoring currently has a Node.js bias (TypeScript, npm audit signals). Python servers may score lower on quality even if well-built. Security scanning works on any language. We're adding Python-specific quality signals.
Is there a free tier?
10 queries per day, no signup, no credit card. Just run the CLI command and it works. Paid plans start at $29/mo for unlimited queries and monitoring alerts. See pricing.
Can I dispute a score?
Yes. Open a GitHub issue or email hello@pulrix.dev. We review disputes within 48 hours. If your server was scored unfairly, we fix it.
You wouldn't npm install a package with 0 downloads and no README.
So why are you connecting MCP servers you found on a random GitHub list?
Check first. Install second.
npx pulrix search "postgres"